Decades-old pre-Stuxnet cyber sabotage tool breaks cover, NSA listed it as 'nothing to see here' — fast16 targeted nuclear reactors, dam design, and other high-precision civil engineering software years before Stuxnet broke cover

Fast16 appears to be at least half a decade older than Stuxnet.
Full article excerpt tap to expand
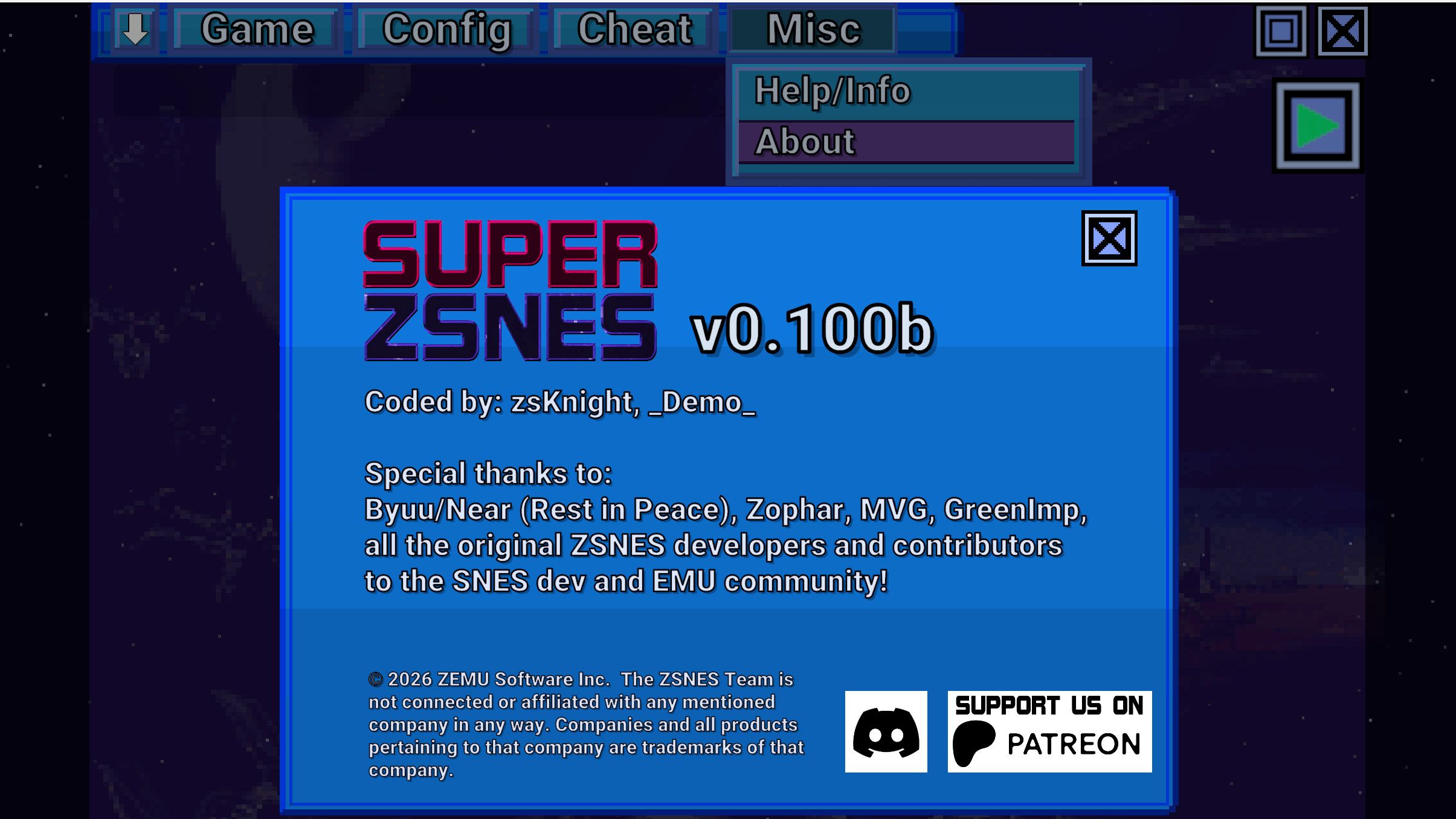
Software Security Software Decades-old pre-Stuxnet cyber sabotage tool breaks cover, NSA listed it as 'nothing to see here' — fast16 targeted nuclear reactors, dam design, and other high-precision civil engineering software years before Stuxnet broke cover News By Mark Tyson published 28 April 2026 Fast16 appears to be at least half a decade older than Stuxnet. When you purchase through links on our site, we may earn an affiliate commission. Here’s how it works. (Image credit: Getty Images) Copy link Facebook X Whatsapp Reddit Pinterest Flipboard Email Share this article 3 Join the conversation Follow us Add us as a preferred source on Google Newsletter Subscribe to our newsletter Security researchers have uncovered a cyber-sabotage platform that predates Stuxnet by at least half a decade. Sentinel Labs has published a blog on their fast16 revelations, discussing the scope of this state-level tool, which targets select high-precision calculation software, slyly introducing inaccuracies. Investigations suggest that fast16 was used to make key calculations in software used for projects involving nuclear reactors, dam design, and broader physics simulations, subtly but reproducibly erroneous.“*** Nothing to see here – carry on ***”Before looking more closely at fast16, it is interesting to ponder who may be behind it and the origin of the name. Sentinel Labs notes that the name ‘fast16’ can be found referenced in an infamous NSA ‘territorial dispute’ file leak. Specifically, it was mentioned in the strongest terms in a do-not-disturb list provided to operators. The line “fast16 *** Nothing to see here – carry on ***” singles out fast16 as being one of - if not the - most important NSA hack tools.The security researchers, including Vitaly Kamluk & Juan Andrés Guerrero-Saade, found fast16 based on an architectural hunch. As a number of high-tier threats in this category were built on an embedded Lua virtual machine, they decided to see if there were traces of earlier Lua VM tools.Article continues below You may like Notepad++ update server hijacked in targeted attacks CanisterWorm, a persistent malware worm, uses time zone to identify and wipe Iranian machines for no apparent reason. Anthropic's latest AI model identifies 'thousands of zero-day vulnerabilities' in 'every major operating system and every major web browser' A file called svcmgmt.exe, which was uploaded to VirusTotal nearly a decade ago, would be a key link. This ‘unremarkable’ file was a 2005 file that was indeed a “Lua-powered service binary.” However, “it still receives almost no detections: one engine classifies it as generally malicious, and even that with limited confidence,” note the security researchers.How fast16 was deliveredThe aforementioned svcmgmt.exe acts as a carrier worm for delivering the fast16.sys kernel driver. It is surprisingly stealthy for a tool of its age. For example, it would check the machine registry for signs of malware monitoring tools from companies like Symantec, TrendMicro, McAfee, etc., to decide whether to abort or to deploy.Spreading of fast16 would occur via wormlets propagating through Windows service control and file-sharing APIs. This version of fast16 targeted Windows 2000 and Windows XP environments and preyed on default and weak admin passwords on file shares.The prime targets of fast16Fast16 was designed to corrupt floating-point calculations in a subtle, predictable, reproducible way. It would seek out executable files, and in…
This excerpt is published under fair use for community discussion. Read the full article at Tom's Hardware.